> |
> That's me working on the next big thing!Established enterprise patching models dead in the water, says report /AI Summit London: AI’s role in UK defence /Government aims to make UK top spot for open source AI /ICO strips commissioner Edwards of responsibilities in HR inquiry /The UK cannot afford a box-ticking solution to cloud dominance /Mythos is turning up the heat on risk, not rewriting the rules /Dutch critical infrastructure lags Europe’s cloud sovereignty divide, SAP executive warns /UK minister for AI calls for more attractive datacentre builds /Lammy announces AI legal assistants for Crown Courts at London Tech Week /ING increases use of AI in mortgage application process /Interview: Pegasystems’ Don Schuerman on how to keep the lid on skyrocketing AI costs /UK government invites experts and industry groups to advise on digital ID plans /Prince William charity and Salesforce set up data lab to tackle homelessness /The politicisation of Silicon Valley /Microsoft smashes record for biggest ever Patch Tuesday update /Enterprises that succeed in agentic AI start by ‘reimagining’ business process, finds Pega research /Inside the AI factory of the future /Councils exit 10-year Capita deal to boost decision and project velocity /Scale of Synnovis breach widens as Essex NHS Trust comes forward /Claude Mythos forces the conversation on defensive AI /
Established enterprise patching models dead in the water, says report /AI Summit London: AI’s role in UK defence /Government aims to make UK top spot for open source AI /ICO strips commissioner Edwards of responsibilities in HR inquiry /The UK cannot afford a box-ticking solution to cloud dominance /Mythos is turning up the heat on risk, not rewriting the rules /Dutch critical infrastructure lags Europe’s cloud sovereignty divide, SAP executive warns /UK minister for AI calls for more attractive datacentre builds /Lammy announces AI legal assistants for Crown Courts at London Tech Week /ING increases use of AI in mortgage application process /Interview: Pegasystems’ Don Schuerman on how to keep the lid on skyrocketing AI costs /UK government invites experts and industry groups to advise on digital ID plans /Prince William charity and Salesforce set up data lab to tackle homelessness /The politicisation of Silicon Valley /Microsoft smashes record for biggest ever Patch Tuesday update /Enterprises that succeed in agentic AI start by ‘reimagining’ business process, finds Pega research /Inside the AI factory of the future /Councils exit 10-year Capita deal to boost decision and project velocity /Scale of Synnovis breach widens as Essex NHS Trust comes forward /Claude Mythos forces the conversation on defensive AI /
ABOUT
Hi I'm Kavi! Recent graduate of Bachelors in Technology in Artificial Intelligence & Data Science. I have been making video games from the age of 14, an experience that gave me strong foundations in computer science and design. I'm currently building AI native B2B SaaS Products and exploring the world of quantitative finance Some quick stats: - Developed 10+ video games - Finalist in 3+ national level hackathons - Served 10+ freelancing clients, valued $300-$5000 per project - Solved 475+ problems on leetcode
Resume.exe
Experience
Lyzr AI
Founder's Office Developer
Aug 2025 - Present | Bengaluru, India (Hybrid)
- Building SaaS applications powered by production ready Lyzr AI Agents
Quantegies
AI Engineer
July 2025 - Aug 2025 | CA, United States (Remote)
- Worked on areas such as quantitative finance, algorithmic trading and machine learning using C++
Teachafy Labs
Founding AI/ML Engineer
Dec 2024 - July 2025 | Chennai, India
- Designed & engineered the product to production, and setup CI/CD pipelines using Git, Docker Compose & AWS
- Ensured 100% consistency integrating 3rd party platforms such as Notion & Frappe, using a two-way database sync system
- Awarded Most Valuable Player of the organization, for completing a four-month project in one month
- Technologies Used: OpenAI Assistants API, Google Agent Development Kit, LangChain, FastAPI, PostgreSQL, Docker Compose, AWS, Composio, Notion, Frappe, Supabase, DevOps, CI/CD
Fiverr
Freelance Full Stack Developer
Dec 2023 - Nov 2024 | Remote, Global
- Delivered 5+ client websites using SvelteKit with 100% on-time completion, and $1.2K revenue in 2 weeks
- Deployed frontend websites with 95-97% mobile performance using optimizations such as caching, lazy loading and splitting
Cognizant
Research & Development Intern
Jun 2023 - Aug 2023 | Chennai, India
- Reduced warehouse navigation time by 50% for clients by innovating an AR navigation app (for Vuzix m400) using Unity3D
- Optimized pathfinding algorithms to enable error-free routing in complex environments, boosting client productivity
- Presented a demo to the President EMEA of Cognizant following internal recognition by high-level executives for work
Selected: Experience
5 Items
Welcome to my
Video Game Universe
VIDEO GAMES
I craft rich purpose driven experience that shares a story, dive into my video game universe! Check out my games at dataoverflow.itch.io
WEB PROJECTS
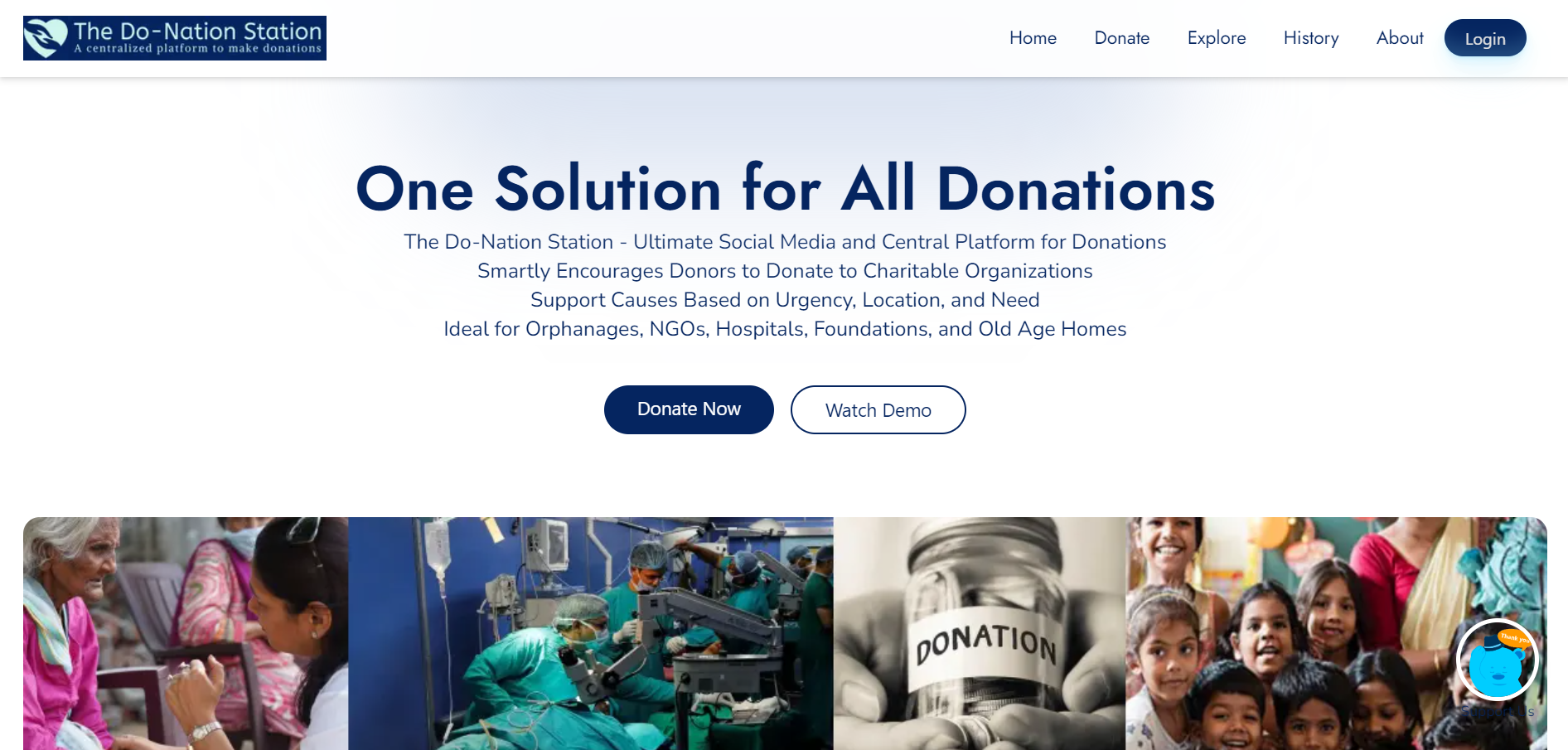
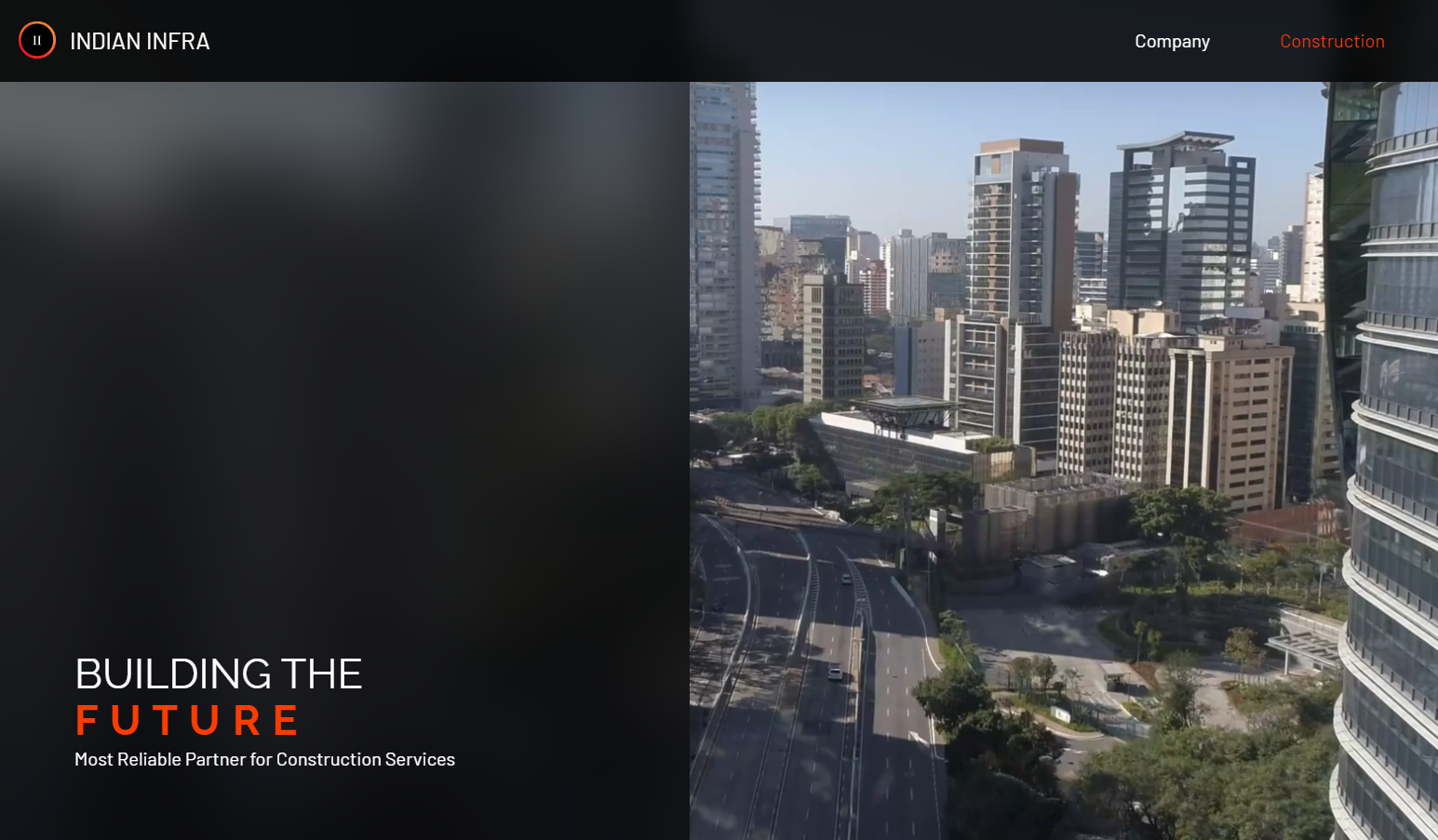
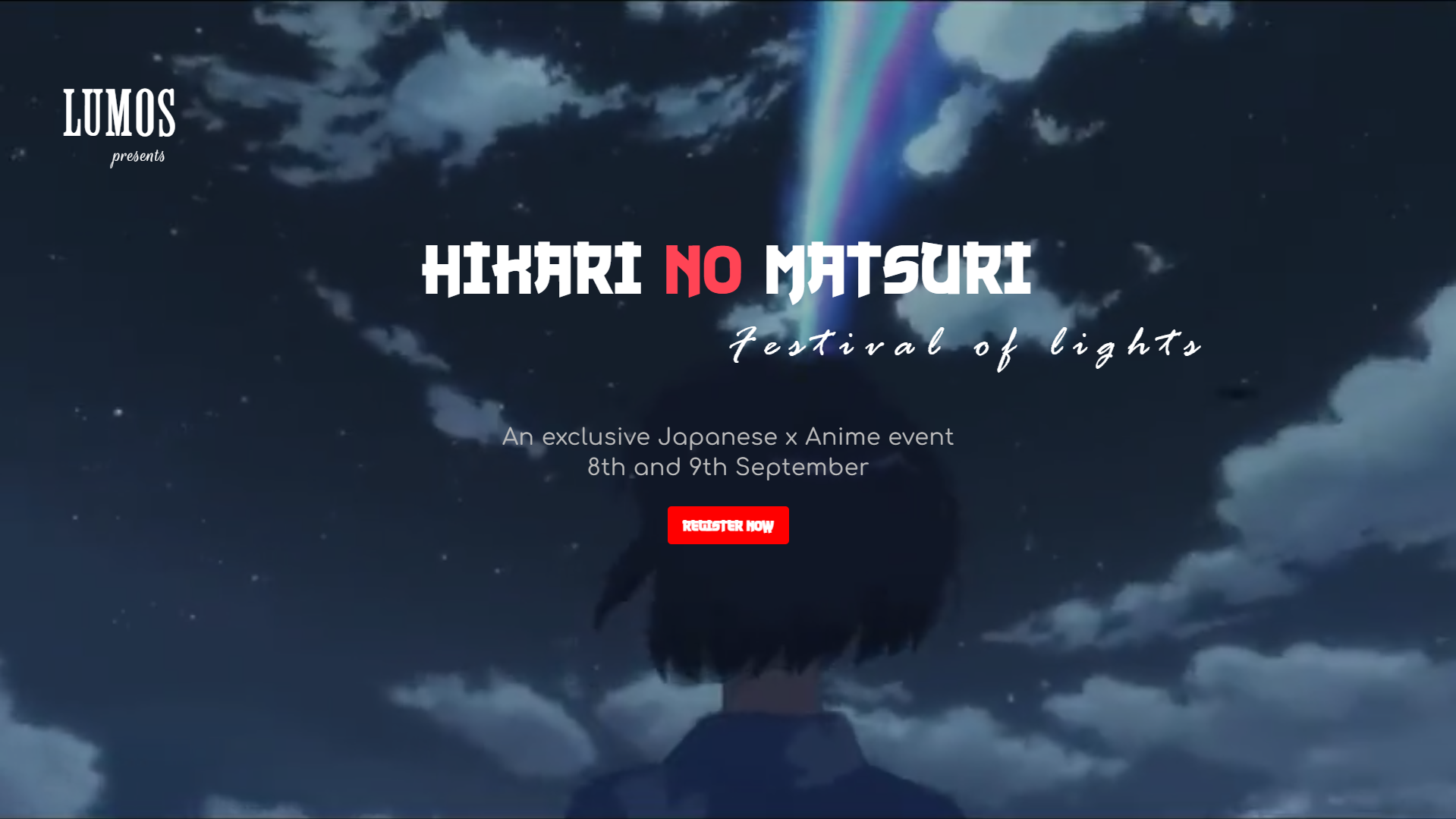
Check out my high performance fullstack projects here
[ ■ ]
All Projects
Open Project (Scroll)
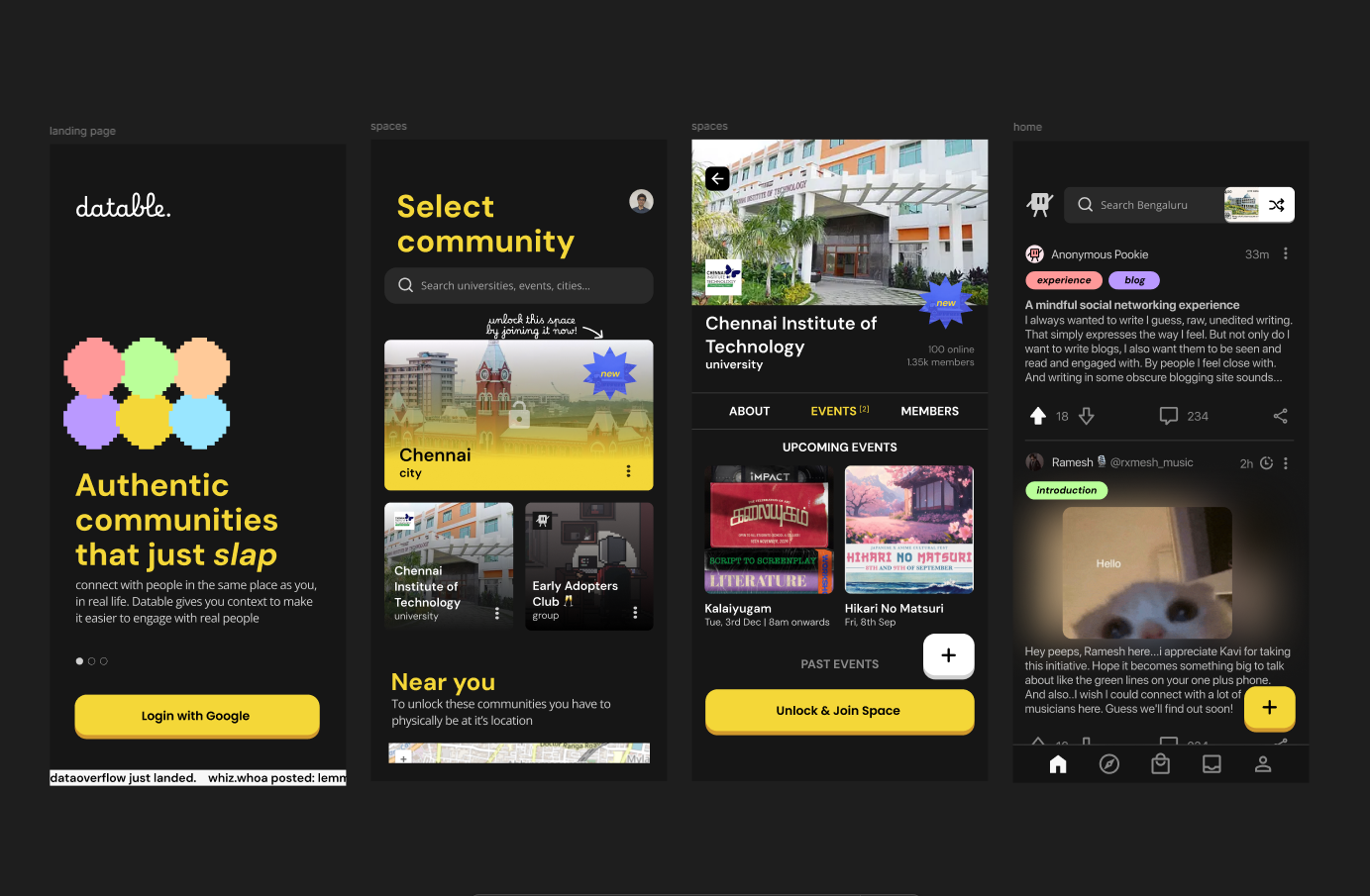
DATABLE - GEOLOCATION SOCIAL APP
SvelteKit 5, Tailwind CSS, Capacitor, Pocketbase, GCP, Docker
Built a community driven platform to augment real life places or events, implementing a recommeder system to meet people. Achieved 99.9% uptime using Docker and GCP, enabling real-time interactions for 100+ active users on the app.
ExploreC:\TURBOC3\BIN\PROJECTS\*CPP
DATABLE.CPP
2024